
Anatomy of Modern Cyber Threat Campaigns
This whitepaper provides a comprehensive analysis of the evolution of cyber campaigns from 2015 to 2025, examining significant milestones, the adoption of emerging technologies like artificial intelligence and quantum computing, and key trends that have defined the modern cybersecurity landscape. Learn more with this free download.

Thoughts on Building a Home Lab?
On LinkedIn we asked: To build a home-lab or not to build a home lab. Waste of time or totally necessary?

Understanding Persistence Techniques in Penetration Testing
Understanding persistence techniques is essential for both attackers and defenders. While penetration testers use them to evaluate security postures, blue teams must recognize and mitigate these risks to maintain system integrity.

Can you be a good pentester without knowing how to code?
Can you become a good pentester without knowing how to code? Let’s hear what our followers on LinkedIn had to say about this.

Post-Penetration Testing Excellence
Penetration testing is a critical step in assessing and improving your organization's cybersecurity posture. Learn more with this free download.

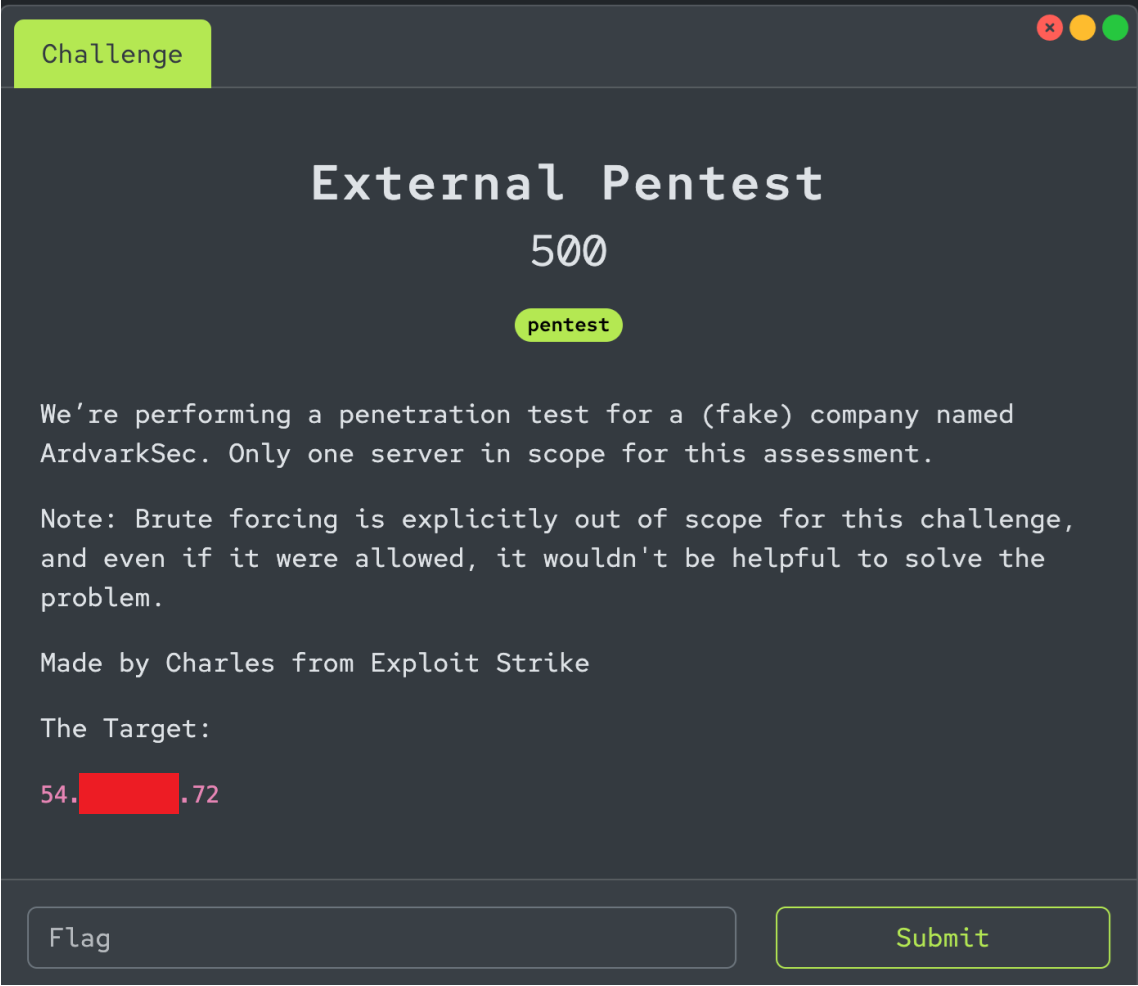
Secure Delaware CTF: External Pentest Writeup
Walkthrough of the external pentest CTF problem that was presented at Secure DE 2024.
